![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
54 Cards in this Set
- Front
- Back
|
What does the SDLC do?
|
- helps ensure functionality, cost, quality, delivery schedule and requirements are met. |
|
|
Name the full SDLC. |
1. Requirements gathering 2. Design 3. Development 4. Testing/Validation 5. Release/Maintenance |
|
|
What is Requirements gathering? |
Determines why, what, whom the software is created for. |
|
|
What is Design? |
- Deals with how the software will accomplish goals. |
|
|
What is Development? |
-Implements software code to meet specifications laid out in the design phase |
|
|
What is Testing/Validation? |
- Validates software product to ensure goals are met and works as planned |
|
|
What is Release/Maintenance? |
-Deploys the software product and ensure that it is properly configured, patched and monitored. |
|
|
What are some software models? |
- Build and Fix Model
- Waterfall - V-shaped - Prototype Model - Incremental Model - Agile |
|
|
Build and Fix Model. Go! |
- Development takes place immediately (no planing) - Problems dealt with as they occur |
|
|
Waterfall Model. Go! |
-linear-sequential life-cycle approach. - phase by phase |
|
|
V-shaped Model |
- Extension of waterfall model. - Emphasizes verification and validation - develops test plans at different development levels |
|
|
What is Verification vs. Validation? |
- Verification: Determines if the product accurately represents and meets the specification - Validation: Determines if the product provides the necessary solution for the intended problem. |
|
|
Prototype Model. Go! |
A sample of software code or a model (prototype) is developed before investing time and and resources. |
|
|
What is Rapid Prototyping? |
quickly develop a prototype to see if their ideas are feasible and move forward. |
|
|
What is Evolutionary prototyping? |
can be continually improved upon until it reaches the final product stage. |
|
|
What is Operational prototyping? |
-an extension of the evolutionary prototype - developed and improved within production environment. |
|
|
What is incremental model? |
- multi-waterfall cycles - each cycle results in a deliverable that is an operational product. |
|
|
What is he Agile model ? Go |
- focuses on individual interaction - emphasizes right software product over comprehensive and laborious documentation - Promotes customer collaboration |
|
|
What are some Programming Languages and Generations? |
• Generation one: machine language - Computer Architecture Specific - 1001011010, etc. • Generation two: assembly language - Computer Architecture Specific - ADD, PUSH, POP, etc. • Generation three: high-level language - Computer Architecture Independent - C, C++, etc. • Generation four: very high-level language - Some are platform-Independent - JAVA, C#, etc. • Generation five: natural language - The goal is to create software that can solve problems by itself instead of a programmerhaving to develop code to deal with individual and specific problems. - Some languages based on advanced knowledge-based processing and artificialintelligence |
|
|
What are some Software Programming Tools? |
- Assembler: >assembly language code into machine code - Compiler >Convert high-level language into the necessary machine level-format (.exe, dll, etc) for specific processors to understand - Interpreter >a tool to convert intermediate, platform-independent format (JAVA bytecode) into a machine-level |
|
|
What are some Software Programming Concepts? |
- Procedural Programming - Object-Oriented Programming (OOP) |
|
|
What does - Object-Oriented Programming (OOP) try to do and avoid? |
- Cohesion - Coupling |
|
|
What is Cohesion? |
- A measurement that indicates how many different types of tasks a module needs to carry out. High cohesion is expected in OOP |
|
|
What is Coupling? |
- A measurement that indicates how much interaction one module requires for carrying out its tasks. Low coupling is expected in OOP |
|
|
What are some types of Software Testing? |
- Unit testing - Integration testing - System testing - Security Testing - Acceptance testing - Regression testing |
|
|
What is Unit Testing? |
-individual component is in a controlled environment - Validating data structure, logic and boundary conditions |
|
|
What in Integration testing? |
- Verifying components work together as outlined in design.
|
|
|
What is System testing? |
- end-to-end testing - tests a full integrated system to verify that it meets its requirements |
|
|
What is security testing?
|
- Focus on security perspectives of the overall system |
|
|
What is acceptance testing? |
-Ensuring the code meets customers requirements |
|
|
What is Regression testing? |
After a change to a system takes place, retesting to ensure functionality, performance and protection |
|
|
What is Software Change Control? and what is the process? |
- the process of controlling the changes that take place during the life cycle. 1. Make a formal request 2. Analyze the request 3. Record the change request 4. Submit the change request for approval 5. Develop the change 6. Report results to management |
|
|
What is software versioning? |
- deals with keeping track of file revisions so it is possible to "roll back" to a previous version |
|
|
When Evaluating a Software Development Process there is a Capability Maturity Model Integration (CMMI) what is it? |
- a model which describes procedures, principles and practices of software development maturity. - vendors use this model to help improve their processes - customers use the model to asses vendors practices. |
|
|
What are the levels of the CMMI? Draw the model |

|
|
|
Why are security issues created in software development? |
Software Vendors - Time-to-time market contraints (no time for security) - Not very easy to show return on security investments Software Development - With complex systems, false assumptions are made when building individual components - Do not have complete insight into vulnerability issues - implement hidden features for self-testing which can create security issues is not cleaned up. Software Operations - Disable security controls/features for usability and performance |
|
|
What are some Secure Software Development Approaches? |
- Requirements gathering - Design - Development - Testing/Validation - Release/Maintenance |
|
|
What is included in the Requirements gathering portion? |
- Security requirements |
|
|
What is included in the design portion? |
- Attack surface analysis - Threat modeling |
|
|
What is included in the development portion?
|
- Computer-aided Software Engineering (CASE) - Static Code Vulnerability Scan |
|
|
What is included in the testing/validation portion? |
- dynamic vulnerability scan - manual security testing |
|
|
What is included in the release/Maintenance |
- Final security review |
|
|
What is an Attack Surface Analysis?
|
- aim to identify and reduce the amount of code and functionality accessible to untrusted users. - attempts to enumerate the list of features that an attacker will try to exploit.
|
|
|
What is an attack surface ? |
What is available to be used by an attacker against the product itself. |
|
|
What is an attack bias? |
-potential attack points that are assigned a value between 0 and 1 based on their assume severity |
|
|
What is a relative attack surface quotient (RASQ)? |
- a relative attackability or likely opportunities for attack against software in comparison to a baseline (introduce by Microsoft) |
|
|
How is RASQ be calculated? |
- the product of the number of attack bias |
|
|
What can RASQ be used for? |
- can be used as a measurement to determine the improvement of code quality and security between version of software. |
|
|
What is Threat Modeling? |
- a systematic approach used to understand how different threats could be realized and how a successful compromise could take place. |
|
|
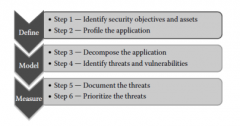
What are the steps of threat modeling? Draw the diagram
|
|
|
|
What is an attack tree? What phase of Threat modeling is this part of? |
- a hierarchical treelike structure, which has either an attacker's objective or a type of attack at its root node. - part of Model phase |
|
|
What is STRIDE? what phase is this part of? |
STRIDE - part of model phase Spoofing Tampering Repudiation Information disclosure Denial of service Elevation of priveldge |
|
|
What is DREAD? What phase is this part pf?
|
DREAD - Measurement Phase Damage Reproducibility Exploitability Affected users Discoverability a risk calculation/ranking. numerica range preferred small (1 to 3) |
|
|
What are some best practices for Software Development Approaches? |
- Web Application Security Consortium (WASC) - best pract for web apps - Open Web Application Security Project (OWASP) - monitor web attacks - Build Security In (BSI) - International Electrotechnical Commission (IEC) - par of ISO/IEC 27000 series |

