![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
21 Cards in this Set
- Front
- Back
|
What is mobile code |
- Code that can be transmitted across a network, to be executed by a system or device on the other end. |
|
|
What are some examples of mobile code? |
-JAVA Applet -Javascript -Adobe Flash Component -Microsoft ActiveX Component |
|
|
In Java Applet Security what are some potential problems? |
- Applet can be easily reverse-engineered
- Applet security manager often run by default rules |
|
|
What are some points about ActiveX Security ?
|
- Uses Authenticode technology, which relies on digital certificates and trusting certificates - Allow web browsers to execute other software applications within the browser -Once allowed to run, they are able to download further ActiveX compoenents without user authentication. -Completely self-sufficient programs that an be executed in Windows environments. -Shared the privilege levels of the current user on a system |
|
|
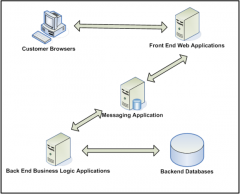
What is the typical architecture or Today's online system? |
- Web-based applications are applications remotely accessible through HTTP protocol. -The most common ports related to web applications are 80 (HTTP) and 443 (HTTPS). |
|
|
Draw the picture of A Typical Architecture of Todays Online System.
|
|
|
|
What can be said about Web Applications and security problems? |
- Web applications are facing directly external attacks - Web applications understand the most application logic from a presentation perspective - Back end applications usually rely on front end web applications to implement many security controls. |
|
|
What is same origin policy (SOP)? |
-it is a key concept applying to client-side web security. - It identifies each website using its origin - orgin is defined as: URL, hostname, port number - It is to allow interactions between resources - Same-origin policy for cookies, DOM access, XMLHttpRequest |
|
|
What is the essential security problem of web applications?
|
- Users have complete control over the client end: - Can submit arbitrary input - Can modify all data passing between browser and server - Can send requests and parameters in any sequence - Can use tools alongside / instead of the browser |
|
|
Vulnerabilities in session management mechanism largely fall into two categories. What are they? |
- Weakness in the generation of session tokens - Weakness in the handling of session tokens |
|
|
What are two types of attacks that involve web applications? |
- Code injection attack - Cross site scripting attack |
|
|
out of those two attacks which ones attack the Same Origin Policy Control? |
Reflected Cross Site Scripting Attack |
|
|
What are some Database security threats? |
- Aggregation Threat - Inference Threat |
|
|
What is an Aggregation threat? |
- Aggregation is the act of combining information from separate sources. - The combination of the data forms new information, which the subject does not have the necessary rights to access. |
|
|
What is an Inference Threat? |
- the ability to derive information no explicitly available. - it is the intended result of aggregation - It is when a subject deduces the full story from the pieces he learned of through aggregation. |
|
|
What are some database security control rules? |
-Content-dependent access control rules -Context-dependent access control rules -Database views -Database locks - Polyinstantiation |
|
|
What is Content-dependent access control rules? |
-access is determined by the sensitivity of the data.
|
|
|
What is Context-dependent access control rules? |
-access is determined by multiple factors such as location, time of day, and previous access history
|
|
|
What are database views? |
- the given set of data a user or group can see when they access the database |
|
|
What are database locks? |
-prevents more than one user from accessing the record at the same time. -prevents edits until the first user finishes |
|
|
What is polyinstantiation? |
-A process used to prevent data inference violations. - prevents low-level database users from inferring higher level data. |

