![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
10 Cards in this Set
- Front
- Back
|
Which statement correctly describes how an ACL can be used with the access-classcommand to filter vty access to a router?
|
An extended ACL can be used to restrict vty access based on specific source addresses, destination addresses, and protocol
|
|
|
Which zone-based policy firewall zone is system-defined and applies to traffic destined for the router or originating from the router?
|
self zone
|
|
|
Which three statements describe zone-based policy firewall rules that govern interface behavior and the traffic moving between zone member interfaces? (Choose three.) |
test |
|
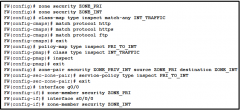
Refer to the exhibit. Which statement is true about the effect of this Cisco IOS zone-based policy firewall configuration? |
The firewall will automatically allow HTTP, HTTPS, and FTP traffic from g0/0 to s0/0/0 and will track the connections. Tracking the connection allows only return traffic to be permitted through the firewall in the opposite direction. |
|
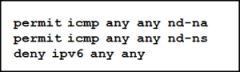
Refer to the exhibit. Which statement describes the function of the ACEs? |
These ACEs automatically appear at the end of every IPv6 ACL to allow IPv6 routing to occur. |
|
|
To facilitate the troubleshooting process, which inbound ICMP message should be permitted on an outside interface? |
echo reply |
|
|
Which statement describes a typical security policy for a DMZ firewall configuration? |
Traffic that originates from the outside interface is permitted to traverse the firewall to the inside interface with few or no restrictions |
|
|
In addition to the criteria used by extended ACLs, what conditions are used by a classic firewall to filter traffic?
|
application layer protocol session information
|
|
|
Which command is used to activate an IPv6 ACL named ENG_ACL on an interface so that the router filters traffic prior to accessing the routing table?
|
ipv6 traffic-filter ENG_ACL out
|
|
|
Class maps identify traffic and traffic parameters for policy application based on which three criteria?
|
access group |

