![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
24 Cards in this Set
- Front
- Back
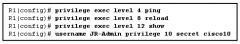
Refer to the exhibit. Which statement about the JR-Admin account is true? |
JR-Admin can issue ping and reload commands. |
|

Refer to the exhibit. What two pieces of information can be gathered from the generated message? (Choose two.) |
This message is a level five notification message. |
|
|
Which three options can be configured by Cisco AutoSecure? (Choose three.) |
enable secret password CBAC |
|
|
What access does role based CLI access for security restrict |
Role-based CLI access enhances the security of the device by defining the set of CLI commands accessible by a specific user. Additionally, administrators can control user access to specific ports, logical interfaces, and slots on a router. This prevents a user from accidentally or purposely changing a configuration or collecting information to which they should not have access. |
|
|
What access does CLI availability restrict? |
role-based CLI access prevents unintentional execution of CLI commands by unauthorized personnel, which could result in undesirable results, and minimizes downtime. |
|
|
What view can configure a root based view |
Only root view |
|
|
What view is a set of commands bundled into a single view |
CLI view |
|
|
What is the purpose of a superview |
It allows an administrator to assign more then one CLI view at once. |
|
|
What features does auto secure enable |
Secure BOOTP, CDP, FTP, TFTP, PAD, UDP, and TCP small servers, MOP, ICMP (redirects, mask-replies), IP source routing, Finger, password encryption, TCP keepalives, gratuitous ARP, proxy ARP, and directed broadcast |
|
|
Which three options can be configured by Cisco AutoSecure? (Choose three.) |
security banner |
|
|
Why is the username name secret password command preferred over the username namepassword password command?
|
It uses the MD5 algorithm for encrypting passwords.
|
|
|
An administrator defined a local user account with a secret password on router R1 for use with SSH. Which three additional steps are required to configure R1 to accept only encrypted SSH connections? (Choose three.)
|
Generate the SSH keys. |
|
|
If AAA is already enabled, which three CLI steps are required to configure a router with a specific view? (Choose three.) |
Associate the view with the root view. |
|
|
What three services does CCP one step lockdown enable |
password encryption |
|
|
Which recommended security practice prevents attackers from performing password recovery on a Cisco IOS router for the purpose of gaining access to the privileged EXEC mode? |
Locate the router in a secure locked room that is accessible only to authorized personnel.
|
|
|
Which statement describes the operation of the CCP Security Audit wizard? |
A security audit feature provided through CCP. The Security Audit wizard provides a list of vulnerabilities and then allows the administrator to choose which potential security-related configuration changes to implement on a router. the wizard is based on the Cisco IOS AutoSecure feature. |
|
|
Which three types of views are available when configuring the role-based CLI access feature? (Choose three.)
|
CLI view superview root view |
|

Refer to the exhibit. Routers R1 and R2 are connected via a serial link. One router is configured as the NTP master, and the other is an NTP client. Which two pieces of information can be obtained from the partial output of the show ntp associations detailcommand on R2? (Choose two.) |
Router R1 is the master, and R2 is the client. The IP address of R1 is 192.168.1.2. |
|
|
What are two characteristics of SNMP community strings? |
SNMP read-only community strings can be used to get information from an SNMP-enabled device.
SNMP read-write community strings can be used to set information on an SNMP-enabled device. |
|
|
Which three areas of router security must be maintained to secure an edge router at the network perimeter? (Choose three.)
|
operating system security
physical security router hardening |
|
|
By default, how many seconds of delay between virtual login attempts is invoked when the login block-for command is configured?
|
one
|
|
|
What is an equivalent of the enable command with SNMP |
set access |
|
|
Which command is used to verify the existence of a secure Cisco IOS image file?
|
dir
|
|
|
What command must be issued on a Cisco router that will serve as an authoritative NTP server?
|
ntp master 1
|

