![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
51 Cards in this Set
- Front
- Back
- 3rd side (hint)
|
When we deploy VoIP there are two important factors
|
Voice Quality of MOS 4 or better.
No blocking, meaning call will go through |
|
|
|
Is there a need for QoS on PSTN?
|
No. PSTN uses circuit switched network and dedicated resources.
VoIP uses packet-switch network where there is contention of multiple stream Contention of voice and data services on the same physical facility. |
|
|
|
What are the drivers for QoS for VoIP?
|
Customers are willing to pay more for QoS service
|
|
|
|
Generally speaking IP is a best effort service. What does best effort mean.
|
There is no priority.
|
|
|
|
The need for QoS
|
A collective measure of the level of services
For a particular application Performance criteria Availability, throughput, connection setup time, percentage of successful transmissions, time to fault detection and correction Bandwidth, packet loss, delay and jitter IP is a best-effort service Well suited to non-real-time data communication To attract and retain paying subscribers Circuit switching has a distinct advantage But ill-suited to other forms of communication IP network: solutions for the QoS are needed Resource-reservation techniques |
|
|
|
Why is MPLS a popular protocol for Service Provider
|
Because MPLS can allow Service Provider to guarantee service
|
|
|
|
TCP and UDP
|
TCP
Error-free, in-sequence delivery But relatively long delay due to acknowledgement and congestion control UDP Fine for transporting voice Provided that Low packet loss No congestion on the network. If there is congestion, some packets are lost. Traffic in the network can be bursty and unpredictable If there is significant packet loss, a speaker may be forced to repeat what he/she just said |
|
|
|
End-to-End QoS
|
QoS must be end-to-end
The support of all network components in the chain Service Level Agreement (SLA) Differentiated services for paying customers Regarding to the type and quality of service to be offered Risk: penalty for failing to meet SLA VoIP and voice over the Internet are not the same (What is the difference?) SLA within the carrier network (Yes) SLA between different carriers (is it possible?) |
|
|
|
Is it possible to have Qos end-to-end
|
Only within a single carriers network.
In the US the internet is a collection of ISP's and is not possible to have end-to-end QoS service |
|
|
|
What are the approaches to QoS?
|
Network over-provisioning - more bandwidth
Network Segregation Separate Voice and Data Networks IntServ and RSVP Reserve the resource before establishing the session DiffServ Categorize traffic into different classes or priorities Real-time applications with higher-priority values |
|
|
|
Network Segregation
Separate Voice and Data Networks |
logical separation of media and control
|
|
|
|
What is RSVP?
|
RSVP is the IP service that allows applications to request end-to-end QoS guarantees from the network. Cisco VoIP applications use RSVP for call admission control, limiting the accepted voice load on the IP network to guarantee the QoS levels of calls. The VoIP Call Admission Control using RSVP feature synchronizes RSVP signaling with H.323 Version 2 signaling to ensure that the bandwidth reservation is established in both directions before a call moves to the alerting phase (ringing). This ensures that the called party phone rings only after the resources for the call have been reserved. Using RSVP-based admission control, VoIP applications can reserve network bandwidth and react appropriately if bandwidth reservation fails.
|
|
|
|
What is DiffServ?
|
Behind all this success is the underlying fabric of the Internet: the Internet Protocol (IP). IP was designed to provide best-effort service for delivery of data packets and to run across virtually any network transmission media and system platform. The increasing popularity of IP has shifted the paradigm from "IP over everything," to "everything over IP." In order to manage the multitude of applications such as streaming video, Voice over IP (VoIP), e-commerce, Enterprise Resource Planning (ERP), and others, a network requires Quality of Service (QoS) in addition to best-effort service. Different applications have varying needs for delay, delay variation (jitter), bandwidth, packet loss, and availability. These parameters form the basis of QoS. The IP network should be designed to provide the requisite QoS to applications.
For example, VoIP requires very low jitter, a one-way delay in the order of 150 milliseconds and guaranteed bandwidth in the range of 8Kbps -> 64Kbps, dependent on the codec used. In another example, a file transfer application, based on ftp, does not suffer from jitter, while packet loss will be highly detrimental to the throughput. To facilitate true end-to-end QoS on an IP-network, the Internet Engineering Task Force (IETF) has defined two models: Integrated Services (IntServ) and Differentiated Services (DiffServ). IntServ follows the signaled-QoS model, where the end-hosts signal their QoS needs to the network, while DiffServ works on the provisioned-QoS model, where network elements are set up to service multiple classes of traffic with varying QoS requirements. Both models can be driven off a policy base, using the CoPS (Common open Policy Server) protocol. Cisco IOS® Software supports both the IntServ and DiffServ models of QoS, along with an optional CoPS-client functionality |
|
|
|
Network Over Provisioning (No QoS)
|
If the issue is congestion, we can over-provision the bandwidth by 200% or more.
With that, there would be no congestion issue. Is it more cost-effective to do over-provisioning than to implement QoS on the network? |
|
|
|
Pro's and Con's of using bandwidth instead of QoS
|
A simplistic but expensive solution
Simple: No major system development Expensive: Significant overbuild Unused for most of the time An inefficient way But, bandwidth is cheap and getting cheaper. Is there really a need for QoS? This debate will continue. |
|
|
|
Moore's Law
|
Moore’s Law
Demand doubles roughly every 18 months Bandwidth availability and bandwidth demand have tended to move almost in lock-step New applications to use the available bandwidth Lesson from the computer memory: Is there a need for paging and other memory management techniques if we have unlimited computer memory? Memory is never enough, so is the bandwidth. |
|
|
|
Advantages of Network Segragation
|
The concern is that the data traffic may congest the network and cause the degradation of the voice service. If we separate voice and data networks, there will be no congestion issue.
Does it contradict the concept of converged networks? It is about virtual segregation and not physical segregation. Technologies VLAN Virtual Circuits (ATM and Frame Relay) MPLS Label Paths |
|
|
|
IEEE 802.1p: LAN Layer 2 QoS/CoS Protocol for Traffic Prioritization
|
IEEE 802.1p: LAN Layer 2 QoS/CoS Protocol for Traffic Prioritization
IEEE 802.1p specification enables Layer 2 switches to prioritize traffic and perform dynamic multicast filtering. The prioritization specification works at the media access control (MAC) framing layer (OSI model layer 2). The 802.1P standard also offers provisions to filter multicast traffic to ensure it does not proliferate over layer 2-switched networks. The 802.1p header includes a three-bit field for prioritization, which allows packets to be grouped into various traffic classes. The IEEE has made broad recommendations concerning how network managers can implement these traffic classes, but it stops short of mandating the use of its recommended traffic class definitions. It can also be defined as best-effort QoS (Quality of Service) or CoS (Class of Service) at Layer 2 and is implemented in network adapters and switches without involving any reservation setup. 802.1p traffic is simply classified and sent to the destination; no bandwidth reservations are established. The IEEE 802.1p is an extension of the IEEE 802.1Q (VLANs tagging) standard and they work in tandem. The 802.1Q standard specifies a tag that appends to an Ethernet MAC frame. The VLAN tag has two parts: The VLAN ID (12-bit) and Prioritization (3-bit). The prioritization field was not defined and used in the 802.1Q VLAN standard. The 802.1P defines this prioritization field. IEEE 802.1p establishes eight levels of priority. Although network managers must determine actual mappings, IEEE has made broad recommendations. The highest priority is seven, which might go to network-critical traffic such as Routing Information Protocol (RIP) and Open Shortest Path First (OSPF) table updates. Values five and six might be for delay-sensitive applications such as interactive video and voice. Data classes four through one range from controlled-load applications such as streaming multimedia and business-critical traffic - carrying SAP data, for instance - down to "loss eligible" traffic. The zero value is used as a best-effort default, invoked automatically when no other value has been set. |
|
|
|
What is the QoS mechanism on the LAN.
|
Networ Segragation using VLAN (802.1P and 802.1Q) to configure virtual LAN's on different subnets
|
|
|
|
What is the QoS mechanism on the WAN?
|
Multiprotocol Label Switch (MPLS) can dynamically configure separate label paths for voice and data traffic.
Different IP subnets for voice and data traffic The bandwidth for the voice traffic can be pre-provisioned and the data traffic will not interfere (or congest) the voice traffic. This is the same as Constant Bit Rate (CBR) for ATM virtual circuits. |
|
|
|
Is there a need for QoS?
|
Yes. because there is network congestion
Over Provisioning Network Segragation RVSP DiffServ |
|
|
|
The design of any network involves seeking a balance between four requirements:
|
The design of any network involves seeking a balance between four requirements:
Meeting the requirements of the traffic demands (capacity): no blocking Meeting the requirements of service features (features) Minimizing the capital and operational cost of the network (cost) Ensuring high network reliability and availability (quality) |
|
|
|
Design Criteria
|
Traffic Analysis and Models
Busy Season Busy Hour (BSBH) The busiest clock hour of the busiest week of the year Scalability Avoiding constant redesigning due to increased traffic Technology Selection SIP or H.323 MGCP vs. MEGACO/H.248 SS7 (legacy, SIGTRAN, SIP-T, etc.) Reliability/Redundancy: network level and service level Voice codec Selection Packetization interval (delay) Silence suppression Call Admission Control (CAC) Blocking: a call request is rejected due to a lack of available bandwidth Is this applicable to VoIP? Who decides to block a call? What are the criteria to block a call? QoS Consideration Dedicated Bandwidth – network segregation QoS at layer2 (802.1p) Others |
|
|
|
Show where BHC/BHCA and Erlang calcualtions are used in the network
|

|
|
|
|
What is Traffic Modeling
|
Based on the traffic demand to calculate the resources to determine the traffic quality
|
|
|
|
Demand, Resources, Quality
|
DEmand is about the callers, Resource is about the trunks, quality is about blocking
|
|
|
|
What is BHCA
|
In telecommunications, busy hour call attempts (BHCA) is a teletraffic engineering measurement used to evaluate and plan capacity for telephone networks. BHCA is the number of telephone calls attempted at the busiest hour of the day (peak hour), and the higher the BHCA, the higher the stress on the network processors. BHCA is not to be confused with busy hour call completion (BHCC) which measures the throughput capacity of the network. If a bottleneck in the network exists with a capacity lower than the estimated BHCA, then congestion will occur resulting in many failed calls and customer dissatisfaction.
BHCA is usually used when planning telephone switching capacities and frequently goes side by side with the Erlang unit capacity calculation. As an example, a telephone exchange with a capacity of one million BHCA is estimated to handle 250,000 subscribers. The overall calculation is more complex however, and involves accounting for available circuits, desired blocking rates, and Erlang capacity allocated to each subscriber. |
|
|
|
What needs to be determined in the Network Topology?
|
How many network elements of a given type will be in each location
Media Gateway (MG) Media Gateway Controller (MGC) Technically, a single MGC could serve all MGs on the network, regardless of the location SIP Proxy Server The bandwidth requirements between those network elements and the outside world How can we allocate bandwidth between network elements (MGs) where the network is a shared resource? |
|
|
|
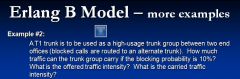
What are the parameters used in the Eralng B Model
|
Erlang-B Model
Traffic Intensity Blocking Probability Number of trunks |
|
|
|
MGC Quantities and Placement
|
A call passes between two MGs controlled
By the same MGC By different MGCs Factors to determine MGC: Call Capacity of MGC Busy Hour Calls (BHC) Number of SS7 and SIP messages that a MGC could handle Delay Requirements of SS7 interoffice delay: <150ms Duration: from an ISUP message entering into an ingress MGC to the ISUP message exiting an egress MGC |
|
|
|
Objectives of Traffic Engineering
|
Users can get dial-tone.
Line Origination Users can make a phone call. Signaling capacity Switch Capacity Trunk Capacity Line Termination What are the reasons that a call fails? Bottleneck, congestion, etc. Where? review the previous diagram |
|
|
|
What are the limiting resources on the network?
|

|
|
|
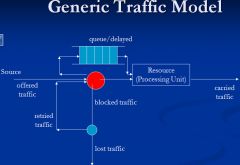
There are three types of traffic flows. When there is no resource there are three possibilities;
1) traffic will be blocked and removed from the network 2) traffic will be blocked and then immediatel will retry 3) the traffic will put in the queue until a resource becomes available What are the Erlang models called for each? |
1) traffic will be blocked and removed from the network.
This is called the Erlang B model 2) traffic will be blocked and then immediatel will retry This is called the extended Erlang B model 3) the traffic will put in the queue until a resource becomes available. this is called the Erlang C model |
In this class we focus on Erlang B where "Blocked Calls are Cleared from the System"
|
|
There are three types of traffic flows. When there is no resource there are three possibilities;
1) traffic will be blocked and removed from the network 2) traffic will be blocked and then immediatel will retry 3) the traffic will put in the queue until a resource becomes available What are the Erlang models called for each? |
1) traffic will be blocked and removed from the network.
This is called the Erlang B model 2) traffic will be blocked and then immediatel will retry This is called the extended Erlang B model 3) the traffic will put in the queue until a resource becomes available. this is called the Erlang C model |
In this class we focus on Erlang B where "Blocked Calls are Cleared from the System"
|
|
|
What defines the Grade of Service?
|
Blocking Probability
Blocking Systems Call request is blocked (i.e. by fast busy signal) if no trunks are available. GoS = Blocking Probability |
|
|
|
What are three Blocking System Examples
What are thre three parameters? |

Resource
Traffic GoS |
|
|
|
What is Holding Time?
|
Holding time = the length of time that a resource is being held (e.g. length of time for a phone call)
What is the average holding time of a residential call? What is the average holding time of a business call? What is the average holding time to any Tech Support? What is the average holding time for an Internet call? |
|
|
|
What is Traffic Volume
|
Traffic Volume for an interval = the sum of all the traffic holding times (of all calls) for that interval
|
|
|
|
What is Traffic Intensity?
|
Traffic Intensity = traffic volume / time interval which is a measure of demand
Traffic Intensity has direction (incoming traffic vs. outgoing traffic) |
|
|
|
Define Traffic Measurement
|

|
|
|

Calculate the erlangs for this example
|

If the usage is in minutes divide by 60. If the usage is in seconds divide by 3600
|
|
|
|
Describe BSBH, HDBH, and ABSBH
|
Circuit traffic is collected for each hour of each day by the Switch’s SPC software. The data is averaged and reported in the following formats:
Busy Season Busy Hour (BSBH): The busiest clock hour of the busiest week of the year The engineering period for applying the GOS criteria. High Day Busy Hour (HDBH) Average traffic during the busiest day of the 10 days (excluding unusual days) in the highest traffic hour. Average Busy Season Busy Hour (ABSBH) The average of 20 BSBH This measurement is applied to trunk groups between COs |
|
|
|
What is A,N,B,C, and U
|

|
|
|

For this example provide the following;
Offered Load Blocking Probability Carried Load Circuit Utlization |

|
|
|
For this example provide the following;
B, N, A, and C |

|
|
|

For this example provide the following;
B, N, A, and C |
|
|
|
|
What is the concept of CAC for VoIP?
|
CAC is needed to ensure quality for accepted calls and block calls when quality cannot be ensured.
|
|
|
|
How is CAC implemented?
|
Performance metrics are required to monitor the network quality. When a performance metric (or a collection of them) is above a thresh-hold value, an incoming call request should be rejected (i.e., a call is blocked.)
This function can be implemented on Call Manager. There are no standards for CAC for VoIP. Can you define a few performance metrics for CAC? What are the thresh-hold values to be used for these metrics? |
|
|
|
What is variable in CAC is the same concept as trunks?
|
the max number of simultaneous calls
|
|
|
|
Describe Call Admission Control (CAC)
|
The network (call manager or softswitch) accepts a call request only if it could guarantee the quality of service (QoS) of the call.
In a network with dedicated bandwidth for VoIP, we can calculate the max number of simultaneous calls based on the allocated bandwidth. This is the parameter N of the Erlang-B model Maximum Call Load When there are N calls in the network, any new call request will be rejected – Same as no trunks are available to route the call. |
|
|
|
How do we caculate bandwidth?
|
VoIP Bandwidth
Voice packet size + 40 octets (for IP, UDP and RTP) + layer 2 overhead RTCP bandwidth should be limited to << 5% of the actual VoIP bandwidth. |
|

