![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
23 Cards in this Set
- Front
- Back
|
Feature Driven Development |
Develop Overall Model - High level walk-through of system scope and context involving the creation of domain models. One or more (combination) of these models is used to become the model for each domain area. Build Feature List - Models created in the first stage are used to compile a list of features. Features should take no longer than two weeks to complete. Plan by Feature - Development plan is produced and ownership of features is assigned. Design by Feature - A design package is produced for each feature. Sequence diagrams are worked out for each feature. Class and method prologues are written followed by a design inspection. Build by Feature - Class owners develop code for their classes. Unit testing and code inspection follow. Each completed feature is promoted to the main build. |
|
|
Test Driven Development Lifecycle |
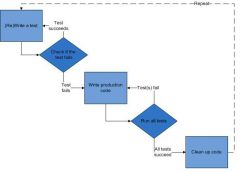
The purpose is to test each component thoroughly before release. |
|
|
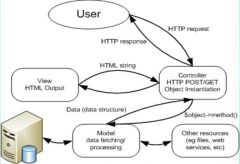
MVC Data Handling |
|
|
|
Encryption |
To transform data to keep it secret from others. The goal is to ensure that the data cannot be seen by anyone other than the recipient(s). This process uses a secret key, the plaintext and the algorithm operation. The ciphertext, algorithm and key are all needed to return the plaintext. Algorithms: AES, Blowfish, RSA |
|
|
Hashing |
Hashing is the process of turning text into a fixed length string of characters that is unintelligible. These cannot be decrypted. Algorithms: SHA-3, MD5 |
|
|
HTTP and Sessions |
HTTP is stateless, meaning that it does not require the server to retain session information or status about each communications partner for the duration of multiple requests. Sessions are employed to overcome this. It acts as a workaround to support session state over a stateless protocol. This is achieved through the use of HTTP cookies. These are small pieces of data sent from the website to the user's computer. |
|
|
Session and Cookie Security Risks |
Cookie Theft - Can be done through XSS by posting malicious code to a website. The code could make a button appear that would (once clicked) send cookie information to a malicious web page. DNS Cache Poisoning - Another way of stealing cookies. By fabricating a DNS entry, an attacker would be able to acquire a users cookies. Session Hijacking |
|
|
Definition: Web Service |
An application developed as loosely coupled software components that is remotely available over TCP/IP. |
|
|
Web Services: Advantages |
- Deployability: Deployed over standard Internet technologies with SSL built in. - Interoperability: Web services allow applications to talk and share data with each other. - Low Cost for Communication: SOAP over HTTP. Low cost option. - Platform Independence: Works on browsers -Provides Functionality to other Services |
|
|
Web Services: Disadvantages |
- Vulnerable to DoS Attacks: The services can be overloaded with too many requests over a short space of time. - Stateless: No information is retained by either sender or receiver. Sessions can be used to work around this. |
|
|
Prepared Statements |
Queries written with placeholders rather than actual values. This means that SQL statement syntax cannot be altered. SQL injection is prevented as a result of this. |
|
|
Behaviour Driven Development: Advantages |
- Provides a common domain language thar everyone understands. - Provides the ability to create test cases prior to development. |
|
|
Behaviour Driven Development: Disadvantages |
- Not suitable for novice developers without TDD knowledge. - Only works with Iterative lifecycle. |
|
|
SLIM |
A micro framework used to write simple and powerful web applications and APIs. Micro-Framework - A lightweight, minimalistic framework. A small and concise code base that addresses a set of use cases and/or problems. Routing - Mapping specific HTTP request methods and URIs to specific callback functions. Behaves as the controller section in MVC. Uses an htacess file for filtering. Middleware - Allows code to be run before and/or after your SLIM application to manipulate the request and/or response. |
|
|
Validation |
Ensuring correct format of user input. |
|
|
Sanitisation |
Removal of illegal characters from user input. |
|
|
Code Example: Prepared Statements |

|
|
|
WSDL Upload/Download from Server |
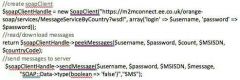
|
|
|
Sanitisation and Validation: Code - Ints |

|
|
|
Sanitisation and Validation: Code - Strings |
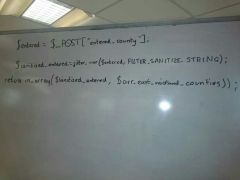
|
|
|
EE M2M Messages |
|
|
|
Latency Causes |
- High Quality Images - Continuous Database Polling - Large File Sizes - Inefficient Code - Geolocation |
|
|
WSDL |
Defines a web service API. Gives the SOAP action URL. Easy way of getting the web details for a service including its methods and location. |

