![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
48 Cards in this Set
- Front
- Back
|
What does POP stand for? |
Post Office Protocol |
|
|
What is POP used for? |
Retrieving emails from server to client, ports 100 & 995 |
|
|
What does IMAP stand for? |
Internet Message Access Protocol |
|
|
Compare POP to IMAP |
IMAP ports 143 & 993 (More advanced) |
|
|
What is SMTP? |
Simple Mail Transfer Protocol, for sending out emails from client to server and email exchanges among servers. Ports 25 & 465 |
|
|
What is MUA? |
Mail User Agent- email client or email reader, e.g/ Microsoft Outlook and Mozilla Thunderbird |
|
|
What protocol does Web Email use? |
HTTP |
|
|
In Email Security what is confidentiality? |
Keep email content secret |
|
|
In email security, what is message integrity? |
prevent and detect modification |
|
|
In email security, what is authentication? |
verify the sender (and hopefully the receiver as well) |
|
|
In email security, what is non-repudiation? |
one cannot deny sending emails |
|
|
Name 3 ways to secure emails |
- simple email encryption -PGP and S/MIME - detect and prevent email phishing |
|
|
Name an example of simple Email Encryption |
Secure Mail for Gmail (by Streak) -- no digital signature -- links are removed -- end to end encyption |
|
|
What is the drawback of Simple Email Encryption? |
Symmetric key. Drawback is getting the password |
|
|
What does PGP stand for? |
Pretty Good Privacy -----Thunderbird +GG4win
|
|
|
What are some Email Spam and Phishing Defense |
Reliable/Trustworthy email providers Identify email senders Double check links Don't download or open unfamiliar attachments Don't forward random emails Report to IT services |
|
|
Name two non-secured protocols that supports password authentication |
rlogin-default TCP port #513 telnet- port #23 |
|
|
What is SSH? |
Secure Shell Supports multiple authentication methods can be used to secure SFTP and SCP Default TCP port #22 |
|
|
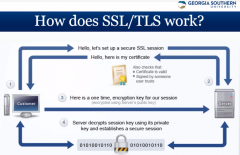
What is SSL? |
Secure Socket Layer Developed by Netscape V.3 published by IETF in 1995, deprecated in June 2015 due to security vulnerability |
|
|
What is TLS |
Transport Layer Security |
|
|
|
|
|
What is FTP and its two ports? |
File Transfer Protocol -port #20 for data -port #21 for control - No encryption -simple user authentication, no server authentication |
|
|
What does SCP stand for? SFTP? FTPS? |
Secure Copy (Port 22) SSH File Transfer Protocol (Port 22) - security level as SSH, ex program WinSCP File Transfer Protocol over SSL/TLS (port 443) |
|
|
What is ISM? And why do we use it? |
(industrial, scientific, medical) unlicensed bands -- Free |
|
|
What is the importance of session establishment? |
-Wifi is based off of this - Clients scan channels to send a broadcast probe request and what for probe responses from access points with SSID Clients sends an authentication and association request to AP |
|
|
What is SSID? BSSID? |
-Service Set Identifier - name of wi-fi -Mac address |
|
|
Name and explain 3 Security Mechanisms |
Hidden wireless networks -omitted SSID in beacons -hide SSID - - BSSID can still be seen -- inSSIDer Mac Filtering Respond to broadcast probe request |
|
|
What can hackers use to find SSID? |
airodump and aireplay |
|
|
What does WEP stand for? WPA? |
Wired Equivalent Privacy (Do Not Use) Wi-Fi Protected Access (Do Not Use)
|
|
|
Types of WPA? |
- WPA2 (802.11i) --default using Advanced Encryption Standard (AES) --TKIP for backward compatibility but not recommended - WPA 2 Personal -- Uses Pre-Shared Key -- PSK used to derive encryption keys -WPA2 Enterprise -- uses authentication server -- WPA2-PSK (TKIP), WPA2-PSK (AES) the current most secure, wPA-PSK(TKIP), WPA-PSK (AES) |
|
|
Other Types of Security Modes |
- Open (Risky) - no passphase - WEP 64 (risky) - vulnerable - WEP128 (Risky) - larger isnt better |
|
|
What Software did was downloaded for Email security? |
Mozilla- Thunderbird Enigmail GnuPG or Linux, Gpg4win (For windows) |
|
|
What was the email software used for? |
Encrypt and Sign emails |
|
|
How do you unlock the secret key in Enigmail? |
Enter in the Passphrase |
|
|
What protocol was used to sign and encrypt the message? |
PGP/MIME |
|
|
What software was used to transfer files between server and client? |
FileZilla |
|
|
What must you NOT have running while operating FileZilla |
other FTP servers (Windows ISS FTP or Apache2Triad) |
|
|
What is the default port number an IP address in FileZilla setup? |
14147 127.0.0.1 |
|
|
What is the default port for FTP server control connection? |
Port 21 |
|
|
Should you leave the default message for FileZilla? Why? |
No, all software has vulnerabilities. IF version number is displayed--easy for hackers |
|
|
What is MODE Z FTP? |
isa real-time compression and transfer protocol under Filetransfercompression |
|
|
What protocol does FileZilla use? |
FTPS (FTP over SSL/TLS) |
|
|
What is the default port number for FTP over TLS? |
990 |
|
|
Sender encrypts emails using symmetric session key (S) S is then encrypted using recipient’s _______ Recipient decrypts S using ___ ____ ____, and decrypts email using ___ Emails signed using sender’s ______ key Recipient verifies signing using sender’s paired _____ key |
- public key -paired private key -S -private -public |
|
|
What does S/MIME Stand for? |
-- Secure / Multipurpose Internet Mail Extension --MIME was developed in the early 90s to allow people to send pictures, sound, programs and general attachments --MIME has no security features -- Standard for signing and encrypting emails |
|
|
What is a digital ID? |
basically same as a digital certificate–your name–public/private key pair–public key certificate for this ID (binding) |
|
|
What is Spam and Phishing? |
Email spam – junk or unsolicited bulk emails --often contain disguised links leading to phishing websites Phishing - a fraudulent process used by spammers to acquire sensitive information from users |
|
|
Name Discovery and Monitoring Tools? |
WiGLE.net: map of APs inSSIDer(or NetStumbler): broadcast probe requests to get responses from AP Kismet: support GPS-tracking, distributed deployment, GUI, a Perl program airodump-ng: part of aircrack-ng war-driving to find APs war-flying with GPS to survey an area |

