![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
20 Cards in this Set
- Front
- Back
|
Explain the function and basic operation of the network application DHCP |
DHCP Is a model for automatically assigning addresses and other configuration parameters to network hosts. |
|
|
Explain the function and basic operation of the network application HTTPS |
In HTTPS another protocol is added called SSL which is used to encrypt and protect data traveling through the network. |
|
|
Explain the function and basic operation of the network application FTP |
Using FTP a client can upload, download, delete or move files on a server. |
|
|
What is ARP ? |
ARP finds a MAC address of a host, from its known IP address. ARP keeps a table where MAC addresses are mapped. |
|
|
How did NAT Prolong the life of IPv4 ? |
NAT conserves the number of globally valid ip addresses a company needs |
|
|
OSI model |
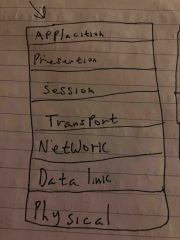
Back (Definition) |
|
|
TCP/IP model e |
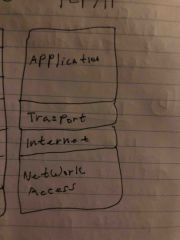
Back (Definition) |
|
|
Main functions of the Transport layer ? |
• The transport layer divides the data into pieces and ads a header for the delivery of the network. • Moves data between applications and devices in the network. • Data for different applications is directed to the correct application because each application has a unique port number |
|
|
What simple mechanism is used For checking errors in the transport header ? |
Flow control. Flow control assist the reliability of TCP transmission by adjusting the effective rate of data flow |
|
|
What is time to live ? |
Time to live is it eight bit binary numbers that indicates the remaining life of a packet. TTL is decreased by one each time the packet is sent by a router, When it becomes 0 to Packet drops |
|
|
What does The packet header protocol mean ? |
Protocol is a bit binary value which indicates the data payload the packet is carrying |
|
|
What is the Checksum In packet header? |
Checksum is to protect the packets against data corruption |
|
|
TCP pros |
TCP is very reliable, guarantees data transfer remains in tact, and arrives in the right order. |
|
|
UDP cons |
UDP is only best effort, unreliable, used in application with fast, officiant transmission, such as games |
|
|
Purpose of Subnet mask ? |
To increase managers control over their address space and makes it easier to allocate the address space, and better network performance. |
|
|
What is VLSM ? |
VLSM is subnetting of a subnet |
|
|
What is meant by CIDR notation in relation to subnet |
CIDR are are used to try and conserve address space as IP addresses are running out |
|
|
What is Segmentation ? |
Segmentation is the process of dividing data packets into smaller chunks for sending over the network |
|
|
What is in Encapsulation ? |
Encapsulation is a process of taking data from one protocol and transferring it to another |
|
|
You can |
Do it |

