![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
79 Cards in this Set
- Front
- Back
|
What key do you use for a Catastrophic Alarm Failure? |
Key 5 |
|
|
What must you authenticate with building custodian before authorizing access to building? |
Owner/user security using last 6 of SSN and authentication matrix. |
|
|
If owner/user does not have authentication matrix, what can they use to authenticate? |
Alarm authentication code. |
|
|
How do you pass an alarm authentication code? |
Pass custodian a number, and wait for them to pass back a number that would add up to the proper authentication code for respected building. |
|
|
What will you never pass for the alarm authentication code? |
Half the number of the alarm authentication code. |
|
|
What do you do after alarm activation is terminated. |
Notify NCOIC, ESS and properly annotate AF Fm 340 |
|
|
If multiple alarms sounds at one time, what must you refer to in order to desperse patrols accordingly? |
Response Priority List. |
|
|
What does ESS stand for? |
Electronic Systems Security. |
|
|
When conducting an alarm test, where will you annotate the given information and results? |
In the Alarm Monitor Pass On Book. |
|
|
What is the first step in assuming post? |
Check the status of all alarms. |
|
|
What are the steps for assuming post? |
Fuel key status, Alarm Monitor key status, gather pass-ons from off going Alarm Monitor. |
|
|
What must you complete during a full Alarm Monitor shift? |
Blotter back, RAM Sheet, Sierra 4/5 check sheet board update, Opening list, and respond to any alarms. |
|
|
What are the Vundicator Strengths l? |
Provides intrusion detection and/or Access Control to controlled/ restricted areas. Visual displays and audible alarms indicate whether an alarm point is in access, secure, or alarm condition. Comm/Power failure conditions are also indicated. |
|
|
What does S.M.A.R.T stand for |
Self Monitoring Analysis and Reporting Technology |
|
|
What are the Vindicator Weaknesses? |
Deteriorating base cables which cause frequent outages causing communications failure and/or intermittent faults; Frequent base power outages cause comm failure between sensors and the annunciator causing equipment to lose synchronization. |
|
|
What are Vendicator Encryption Capabilities? |
Ultra High Security (UHS) single; Data Encryption Standard (DES) triple encrypted; DES/Triple Data Encryption Algorithm (TDEA) |
|
|
What is Ultra High Security (UHS) |
Uses proprietary encryption residing in firmware; communication with other UHS devices and DES-net SMART systems. |
|
|
What is DES/Triple Data Encryption Algorithm (TDEA)? |
Encrypted IAW FIPS Pub 46-3 TDEA algorithm; communications with other DES-TDEA-net devices and minimally with UHS-net gateways. |
|
|
What do the Vindicator Class 1 and 2 Line Supervision use? |
Uses Director of Central Intelligence Directive (DCID) and National Institute of Standards and Technology (NIST). |
|
|
What does the encryption capabilities of DCID and NIST provide? |
Class 1 supervision of four transmission lines leaving restricted area and trans versing an uncontrolled area. |
|
|
What does the encryption capabilities of the V5 Vindicator provide? |
Class 2 supervision to each sensor connected to the system. |
|
|
The Vindicator SMART system conducts all polling for what system? |
Vindicator V5 System. |
|
|
Who is authorized to monitor the Vindicator alarm system? |
Only trained and certified Alarm Monitors. |
|
|
Who will operate remote keypads at alarmed facilities? |
Only trained and certified personnel whom are authorized and listed in the AAL for their respective buildings inside Alarm Book. |
|
|
No food, drink, or personnel items will be stored where? |
On the alarm console or near the Uninterruptible Power Supply (UPS) |
|
|
What are the Alarm Types? |
Balanced magnetic switch (BMS) Switch mode power supply (SMPS) Microwave intruder detection (PIR) Junction box TAMPER Security Access Code (SECACC) Duress |
|
|
How many Alarm Types are there? |
Six |
|
|
True or False: SMPS A/C Power Fail is not an alarm. |
True |
|
|
What alarm usually follows a PIR? |
Perimeter/BMS |
|
|
True or False: you must dispatch a patrol to a PIR alarm regardless if BMS alarm was activated. |
True |
|
|
What are PIR alarms useful in tracking? |
An intruders progress through a facility. |
|
|
What should responding patrols be notified of as each trap/PIR alarm is received and why? |
They should be notified which alarm point is being set off, because if they must enter the facility they will know the general location of the intruder. |
|
|
Where are junctions boxes located? |
Not strictly located at the facilities themselves but may be located throughout the base. |
|
|
What should TAMPER boxes be locked with? |
High security padlock |
|
|
What are the three types of duress buttons? |
Remote. Hardwire. Keypad. |
|
|
Alarm colors? |
Red- activation of interior device. Blue- power/comm failure. Green- alarm point is secure. Yellow- alarm is accessed. Magenta- tamper alarm. |
|
|
How many colors are the alarm codes broken down into? |
Five |
|
|
What can the sound from an alarm tell you? |
What type of alarm you are receiving without looking at the screen. |
|
|
What does the asterisk (*) next to an alarm mean? |
The alarm is still active. |
|
|
What will the Alarm Monitor check to know if someone is within the area? |
By checking for an asterisk at any given location. |
|
|
What does it neb if an asterisk is next to a PIR? |
Something is inside the area moving around. |
|
|
What does it mean if an asterisk is next to a BMS? |
This indicates an open door. |
|
|
How can the Alarm Monitor pass information to responding patrold to the whereabouts of individuals inside a facility? |
By tracking movements using the PIRs and BMSs |
|
|
When must SF patrols be despatched for an alarm? |
When the Alarm Monitor cannot determine the cause of an alarm via IVA or posted sentry. |
|
|
Where are the function keys of the S.M.A.R.T. located? |
On the right monitor and keyboard. |
|
|
How are the function keys of the S.M.A.R.T. identified on the screen? |
On the right monitor and keyboard. |
|
|
How are function keys of the S.M.A.R.T. identified on the screen? |
As a tab, or as a button |
|
|
What are function keys "F1" through "F6" known as? |
Dynamic keys. |
|
|
When an alarm annunciates, what will the operator's first action be. |
Acknowledge the alarm using F1 |
|
|
What does pressing F1 do (besides acknowledging the alarm)? |
Silences the alarm |
|
|
What the options does the operator have after acknowledging the alarm? |
Secure, Access, and Tag |
|
|
When will the operator have to secure, access, or tag a facility? |
For facilities without an entry/exit keypad |
|
|
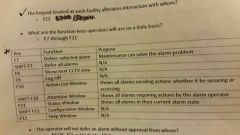
Function keys? |
|
|
|
The keypad located at each facility alleviates interaction with whome? |
ECC |
|
|
What are the function keys operators will use on a daily basis? |
F7 through F11 |
|
|
The operator will not defer an alarm without approval from whom? |
NCOIC, ESS or Vindicator NCO |
|
|
Deferring alarms will be made on what type of basis? |
Case by case basis |
|
|
True or False: Operators will not attempt to configure the system. |
True |
|
|
Where are the VCC console controls located? |
Center monitor and keyboard |
|
|
How many sections is the VCC screen broken down into? |
Three |
|
|
Upon request from a facility to conduct an alarm check, what will Alarm Monitors log? |
Name of custodian Name of Alarm Monitor Type of alarms tested Building Date |
|
|
Can you refuse an alarm test? |
No, unless you are busy with other incidents. |
|
|
What will the Alarm Monitor do before the alarm test is conducted? |
Authenticate with the custodian |
|
|
After Alarm Monitor authenticates with custodian for an alarm test, what will the custodian state? |
What alarm is to be tested. |
|
|
What alarms must be tested for an alarm test? |
Intrusion, detection, and duress if installed |
|
|
What are all posts with duress systems installed required to do with the alarm monitor at the beginning of each shift? |
Conduct a duress check. |
|
|
Where will the duress checks be annotated? |
SF Blotter |
|
|
If no contact is made inside of a facility after an alarm, how will you attempt to make contact with a custodian? |
Contact custodian at their residence |
|
|
If contact cannot be made with the facility custodian listed on the Alarm Facility sheet located in the alarm book, what will you do? |
Contact the responsible commander |
|
|
What is a Nuisance Alarm? |
When you receive two or more nuisance alarms from the same facility or structure within a 24-hour period |
|
|
Who must you notify of a nuisance alarm? |
NCOIC, ESS |
|
|
Who would you notify if there is a nuisance alarm for a facility that is a controlled area? |
NCOIC, Resource Protection |
|
|
If communication failure resets itself, what will you do as a response? |
Continue with the response as normal |
|
|
What is Human Error caused by? |
The action of the owner/user |
|
|
What will human error result in? |
The accomplishment of a Human Error Worksheet |
|
|
What will the Alarm Monitor do in the case of a system failure? |
All owner/users of protected facilities will be contacted and instructed to assume security of their facilities |
|
|
Which facilities will be given response priority? |
Facilities which store arms and ammunition |
|
|
Facilities which store arms and ammunition misty be protected by whom and until when? |
An armed guard until the alarm system is repaired |
|
|
What will Alarm Monitors do immediately after calling owner/users and sending out guards? |
Contact NCOIC, ESS for further guidance |

